Key Takeaways:
- Expert Driven Testing Matters Most. Top-rated penetration testing vendors use realistic, manual testing methodologies that mirror actual cyber attacker tactics, focusing on context-rich analysis and actionable results far beyond automated scans or compliance checklists.
- Real Penetration Testing Delivers Tangible ROI. A genuine penetration test costing $20,000 to $40,000 for SMBs can mitigate breaches that average $4.8 million in damages per incident, demonstrating an ROI exceeding 12,000% when effective security is implemented.
- Vendor Selection Requires Deep Due Diligence by Both Sides. The best penetration test companies avoid pricing based solely on IPs, URLs, or seats and instead scope projects according to the real attack surface and customer objectives.
- Industry Leadership and Specialty Sets Leading Firms Apart. Top vendors stand out for credentials, thought leadership, reporting clarity, technical depth in areas like social engineering, identity infrastructure, and embedded systems. Many have published research and tools, spoken at major conferences, and offer flexible solutions for diverse business needs.
- Long-Term Security Partnership Is the Goal. Elite penetration testing firms emphasize knowledge transfer, transparent reporting, and ongoing advisory relationships – transforming the engagement from a one-time transaction into an enduring security partnership for clients.
The General Data Protection Regulation (GDPR) establishes strict requirements for organizations that process personal data of EU residents. While GDPR does not explicitly mandate penetration testing (similar to SOC 2), Article 32 requires organizations to regularly test and evaluate the effectiveness of their security measures. The accepted method for this testing is penetration testing.
Auditors and regulators expect more than automation-heavy tests. Vulnerability scans and AI-driven penetration testing tools have their place, but they don’t prove your defenses work against a skilled attacker. If your penetration test looks like a checkbox exercise, auditors may reject it and require retesting with a vendor that delivers realistic, expert-led testing. Don’t put yourself in a position where you’re paying for two penetration tests, do it right the first time. This article explains GDPR requirements, how penetration testing supports compliance, and what your organization needs to do in 2026.
What is GDPR in Cybersecurity?
GDPR is a data protection law enacted by the European Union that governs how organizations collect, process, store, and protect personal data of individuals in EU member states. From a cybersecurity perspective, GDPR requires organizations to implement technical and organizational measures that properly safeguard data confidentiality, integrity, and availability (CIA).
The regulation applies to any organization, regardless of geographic location, that processes personal data of EU residents. This includes companies based in the United States, Asia, or anywhere else that handles EU data subject information.
GDPR’s cybersecurity centers focus on:
- Protecting personal data against unauthorized access, disclosure, or destruction
- Implementing appropriate security controls based on risk assessment
- Regular testing, assessing security measures to ensure ongoing effectiveness
- Responding to breaches within 72 hours of discovery
Critically, non-compliance carries heavy penalties of up to €20 million or 4% of annual global turnover, whichever is higher. Considering these penalties, the ROI of high-quality penetration testing is massive if it prevents even a single breach. Equally massive are the risks associated with settling for a checkbox test.
GDPR Cybersecurity Requirements You Must Follow
Article 32 of GDPR outlines the core GDPR requirements. It mandates that organizations implement “appropriate technical and organizational measures to ensure a level of security appropriate to the risk.” In this context, appropriate is synonymous with the level of threat your organization is likely to face in a real-world attack scenario. For this reason, threat-led penetration testing is the ideal match for GDPR.
Encryption and Pseudonymization
GDPR explicitly recommends encryption as a security measure. Organizations should encrypt personal data both at rest and in transit. Pseudonymization of processing data is also recommended so it cannot be attributed to a specific individual without additional information, it provides another layer of protection.
Confidentiality, Integrity, and Availability
Organizations must ensure ongoing confidentiality, integrity, availability, and resilience of processing systems and services. This encompasses access controls, data validation, redundancy, and disaster recovery planning.
Restoration and Recovery Capabilities
GDPR requires the ability to restore access to personal data in a timely manner following a physical or technical incident. Backup systems, incident response plans, and business continuity measures are essential.
Regular Testing, Assessing, and Evaluating
Article 32(1)(d) requires “a process for regularly testing, assessing and evaluating the effectiveness of technical and organizational measures for ensuring the security of the processing.” This is where services like threat-led penetration testing become critical, they provide the evidence that your controls actually work when challenged with real-world attack scenarios.
Does GDPR Require Penetration Testing?
Direct Requirements vs. Expectations
GDPR does not explicitly require penetration testing by name. The regulation uses principles-based language, requiring “appropriate” security measures and “regular testing” without specifying exact methodologies.
However, regulators and auditors interpret Article 32’s “regular testing” requirement to include realistic penetration testing, not just automated scans or AI. The UK Information Commissioner’s Office (ICO) specifically recommends penetration testing to “simulate real-world attacks and assess the system’s resilience.” When demonstrating compliance, organizations must provide evidence that their security controls can withstand actual attack scenarios, not just pass vulnerability scans or AI penetration tests.
In practice, high-quality threat-led penetration testing has become an expectation for organizations processing significant amounts of personal data or sensitive categories of data. Auditors want to see that you’ve tested your defenses realistically, the way real attackers would test them.
Why Vulnerability Scanning Alone Is Not Enough
A significant gap exists between when vulnerabilities or attack techniques are discovered and when they become public domain. A second gap exists between when they become public and when they are integrated into automated tools. Because automated technologies like vulnerability scanners and AI are only capable of testing for known vulnerabilities, their coverage is directly affected by this gap.
Additionally, automated systems cannot replicate a skilled human attacker because they lack creativity, intuition, and the ability to learn from experience. For these reasons, organizations should be wary of vendors that depend heavily on automation to satisfy GDPR’s testing requirements.
Vulnerability scanning and AI fall short because:
- They can only detect known vulnerabilities, leaving coverage gaps for zero-days and emerging attack techniques
- They miss business logic flaws and chained attack paths that require human reasoning
- They cannot test human factors like susceptibility to social engineering
- They generate false positives and false negatives that require human verification
- They cannot reliably demonstrate actual exploitability or real-world impact
- They lack the intuition and creativity that skilled human attackers bring to every engagement
Genuine, realistic threat penetration testing is conducted by skilled human testers and validates whether your security controls can prevent, detect, and contain real attacks. This provides the evidence auditors need to confirm your Article 32 compliance. 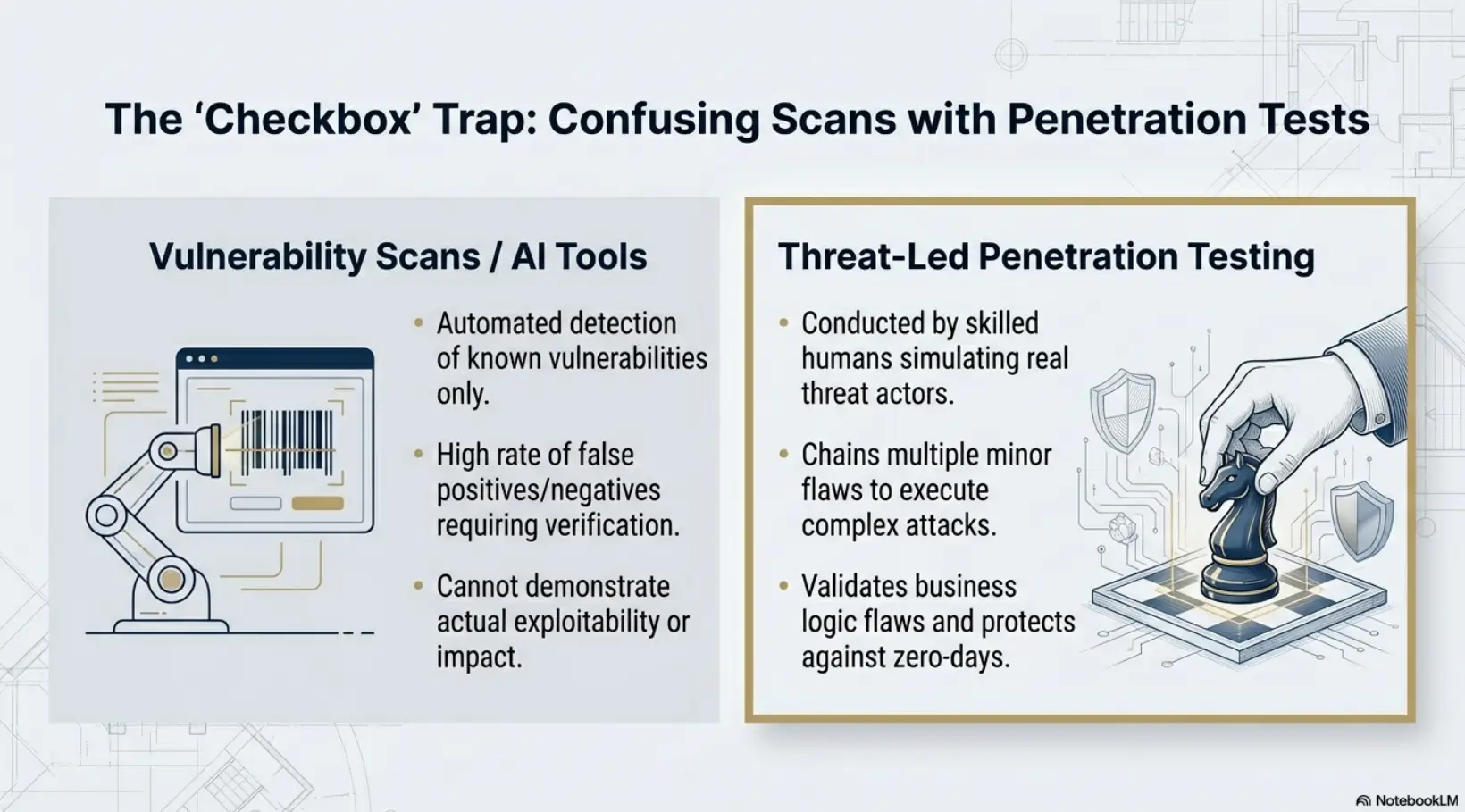
GDPR Penetration Testing Requirements
Organizations subject to GDPR should conduct realistic threat penetration testing that covers all systems processing personal data. This includes systems that collect, store, transmit, or display personal data but the scope doesn’t stop there. Adjacent systems that can access personal data, even if they don’t routinely process it, should also be tested.
These adjacent systems are what form the chain for the path to compromise. They can include administrative interfaces, backup systems, and third-party integrations with access to personal data environments and more. The scope and frequency of testing depend on your risk profile, data sensitivity, and regulatory expectations.
Types of Penetration Testing for GDPR Environments
- External Penetration Testing: Tests internet-facing systems and network perimeters that could expose personal data
- Internal Penetration Testing: Emulates insider threats or compromised credentials to test access controls around sensitive data
- Web Application Testing: Identifies vulnerabilities in applications that collect, display, or process personal data
- API Testing: Evaluates security of Application Program Interfaces that transmit personal data between systems
- Cloud Security Testing: Assesses configurations and access controls in AWS, Azure, GCP, or other cloud environments storing personal data
- Social Engineering Testing: Tests employee awareness and organizational defenses against phishing, pretexting, and other human-targeted attacks
How Often Should You Test?
GDPR requires “regular” testing but does not specify frequency. The reality is defenders need to get it right every time while attackers only need to get it right once. Test frequency should match the pace at which new security vulnerabilities are introduced.
Industry best practices recommend:
- Annual penetration testing at minimum for all systems processing or within proximity to personal data
- Testing after significant changes to infrastructure, applications, or business processes
- Testing following security incidents to validate remediation effectiveness
- More frequent testing for high-risk environments processing sensitive data categories
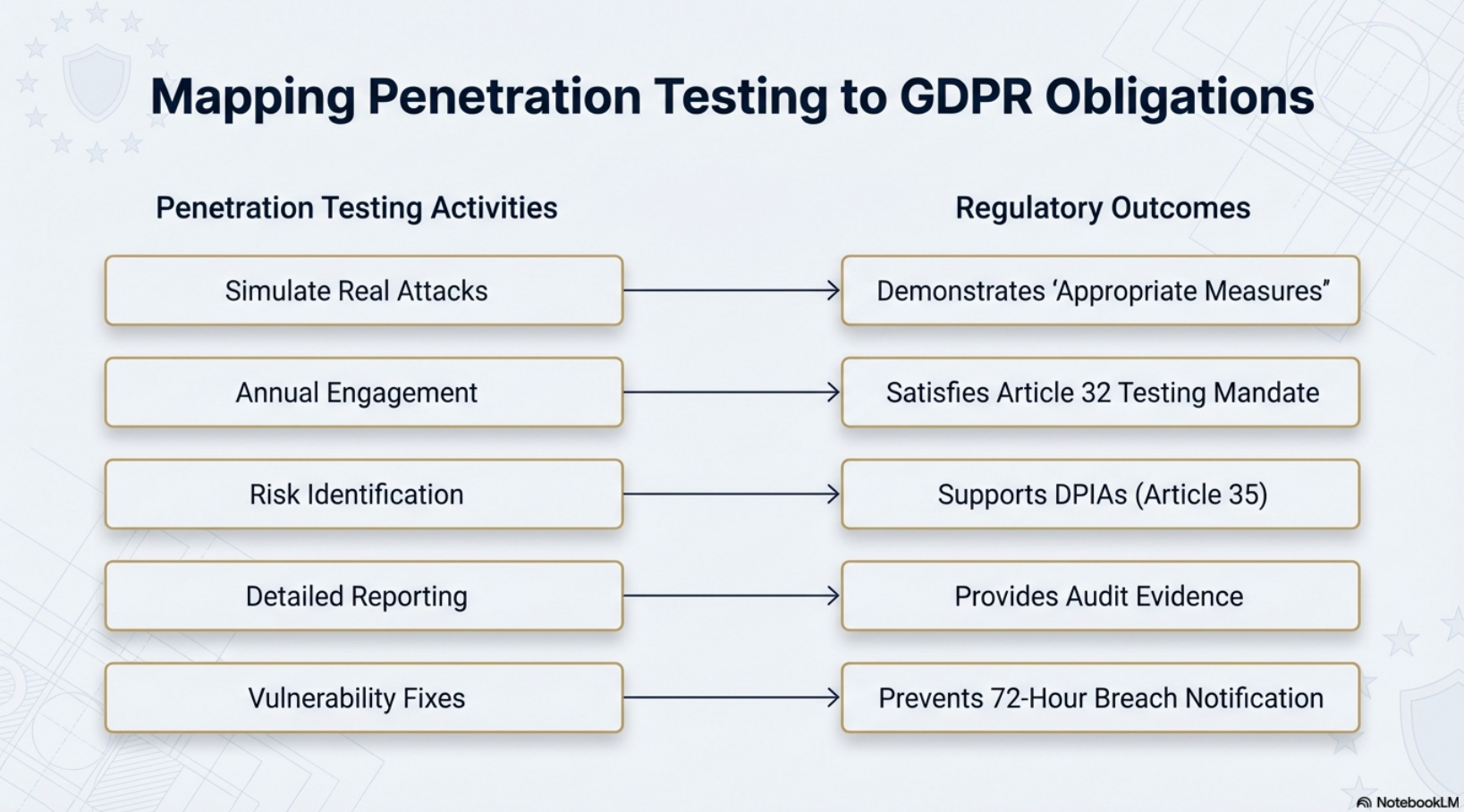
How Penetration Testing Supports GDPR Compliance
Penetration testing directly supports multiple GDPR requirements:
- Demonstrates “appropriate” security measures —Testing proves your controls are proportionate to the risks you face
- Satisfies the testing requirement — Article 32(1)(d) mandates regular evaluation of security effectiveness
- Supports Data Protection Impact Assessments (DPIAs) — Penetration test results inform risk assessments required under Article 35
- Provides audit evidence — Detailed reports document your security posture for regulators
- Identifies vulnerabilities before attackers do — Proactive testing helps prevent breaches that trigger 72-hour notification requirements
GDPR Cybersecurity Checklist for 2026
Use this checklist to assess your organization’s GDPR cybersecurity posture across data protection, technical controls, testing, and response readiness.
Data Protection Foundations
- Completed data mapping to identify all personal data processing activities
- Documented lawful basis for each processing activity
- Appointed Data Protection Officer (if required)
- Established data retention policies and deletion procedures
Technical Security Measures
- Implemented encryption for data at rest and in transit
- Deployed access controls based on least-privilege principles
- Configured network security controls (firewalls, segmentation)
- Enabled logging and monitoring for systems processing personal data
- Secured endpoints with anti-malware and patch management
Testing and Assessment
- Conducted annual penetration testing of systems processing personal data
- Performed vulnerability assessments with validated remediation
- Completed Data Protection Impact Assessments for high-risk processing
- Documented test results and remediation actions for audit evidence
Incident Response and Recovery
- Developed breach notification procedures (72-hour timeline)
- Tested incident response plan through tabletop exercises
- Implemented backup and recovery procedures for personal data
- Established communication templates for data subjects and authorities
Third-Party Management
- Executed Data Processing Agreements with all processors
- Conducted security due diligence on third-party vendors
- Verified sub-processor compliance with GDPR requirements
Training and Awareness
- Provided GDPR awareness training to all employees
- Conducted phishing simulations and security awareness exercises
- Trained staff on data subject rights and request handling
Why Choose Netragard for Your GDPR Penetration Test
Since 2006, Netragard has delivered Realistic Threat Penetration Testing (aka Threat-Led Penetration Testing) that goes far beyond automated scanning to identify real and impactful vulnerabilities in your environment. Our approach directly supports GDPR compliance by providing auditors with the evidence they expect.
Contextualized Threat Intelligence
We analyze threats specific to your industry and data processing activities. Testing scenarios reflect how actual attackers would target personal data in your environment. We do not follow generic vulnerability checklists.
Comprehensive Testing Coverage
Our team tests external networks, internal systems, web applications, APIs, cloud environments, and human factors. We use a research-based methodology called Real Time Dynamic Testing™ to identify areas of weakness that automated scanners and AI will miss. [Explore Netragard’s Penetration Testing Services]
Audit-Ready Documentation
Our detailed reports provide executive summaries, technical summaries, technically detailed findings, carefully calculated risk scores, and tailored remediation guidance. You receive the evidence needed to demonstrate Article 32 compliance to regulators and auditors.
Remediation Validation
We provide free retesting to verify that the deployed fixes not only work but also that they don’t introduce new weaknesses. This demonstrates your security improvements are effective and provides additional evidence of compliance.
Ready to validate your GDPR security controls?
FAQ
Does GDPR require penetration testing?
GDPR does not explicitly require penetration testing by name. However, Article 32(1)(d) mandates “a process for regularly testing, assessing and evaluating the effectiveness of technical and organizational measures.” Regulators and auditors interpret this to include penetration testing, especially for organizations processing significant volumes of personal data or sensitive data categories. In practice, penetration testing has become an expected component of GDPR compliance programs.
What is Article 32 of GDPR?
Article 32 is the GDPR provision that establishes security requirements for organizations processing personal data. It requires implementing “appropriate technical and organizational measures” to ensure security proportionate to the risk. Specific requirements include encryption and pseudonymization, ensuring confidentiality, integrity, availability, and resilience of systems, restoring access to data after incidents, and regularly testing security measures. Article 32 forms the legal basis for GDPR’s cybersecurity expectations.
Is ISO 27001 the same as GDPR?
No. ISO 27001 is a voluntary international standard for information security management, while GDPR is a mandatory EU regulation focused on data protection and privacy. ISO 27001 covers all information assets and security practices; GDPR specifically protects personal data of EU residents. While ISO 27001 certification supports GDPR compliance, particularly the security requirements in Article 32, it does not cover all GDPR obligations such as consent management, data subject rights, or breach notification. Organizations often use ISO 27001 as a framework to meet GDPR’s technical requirements while implementing additional controls for privacy-specific obligations.
What is GDPR and CCPA in cybersecurity?
GDPR (General Data Protection Regulation) and CCPA (California Consumer Privacy Act) are both data protection laws that include cybersecurity requirements. GDPR applies to organizations processing personal data of EU residents and requires implementing appropriate security measures under Article 32. CCPA applies to businesses handling California residents’ personal information and requires “reasonable security procedures.” Both laws mandate protecting personal data from unauthorized access, though GDPR provides more specific security guidance. Organizations subject to both regulations often find significant overlaps in security controls, with GDPR typically setting the higher standard.